Your IP address identifies you
Every device connected to the internet uses an IP address assigned by a network provider. This address enables connectivity, but it also acts as a persistent identifier. Over time, it can be used to correlate activity, build profiles, and associate behavior with a physical location or household.
When you browse without a VPN, your IP address is visible to websites, services, and intermediaries by default. Even without logging into an account, repeated connections from the same address make long-term correlation trivial.
A VPN replaces your public IP with one controlled by the VPN provider, breaking the direct link between your device and the destinations you access.
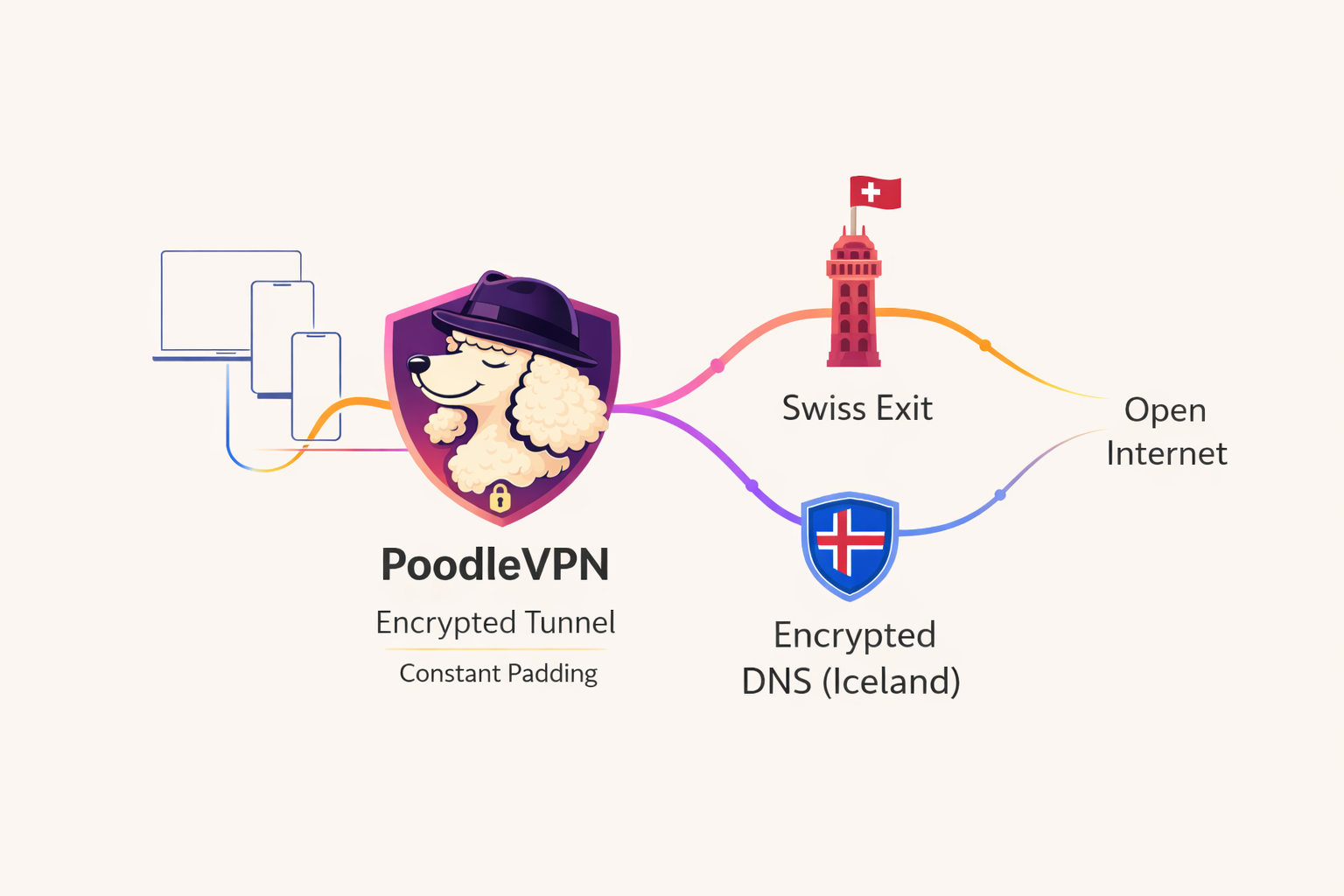
 POODLEVPN
POODLEVPN