Your IP Address Reveals Identity
Every internet-connected device receives an IP address from its provider, creating a persistent network identifier that can be correlated across sessions.
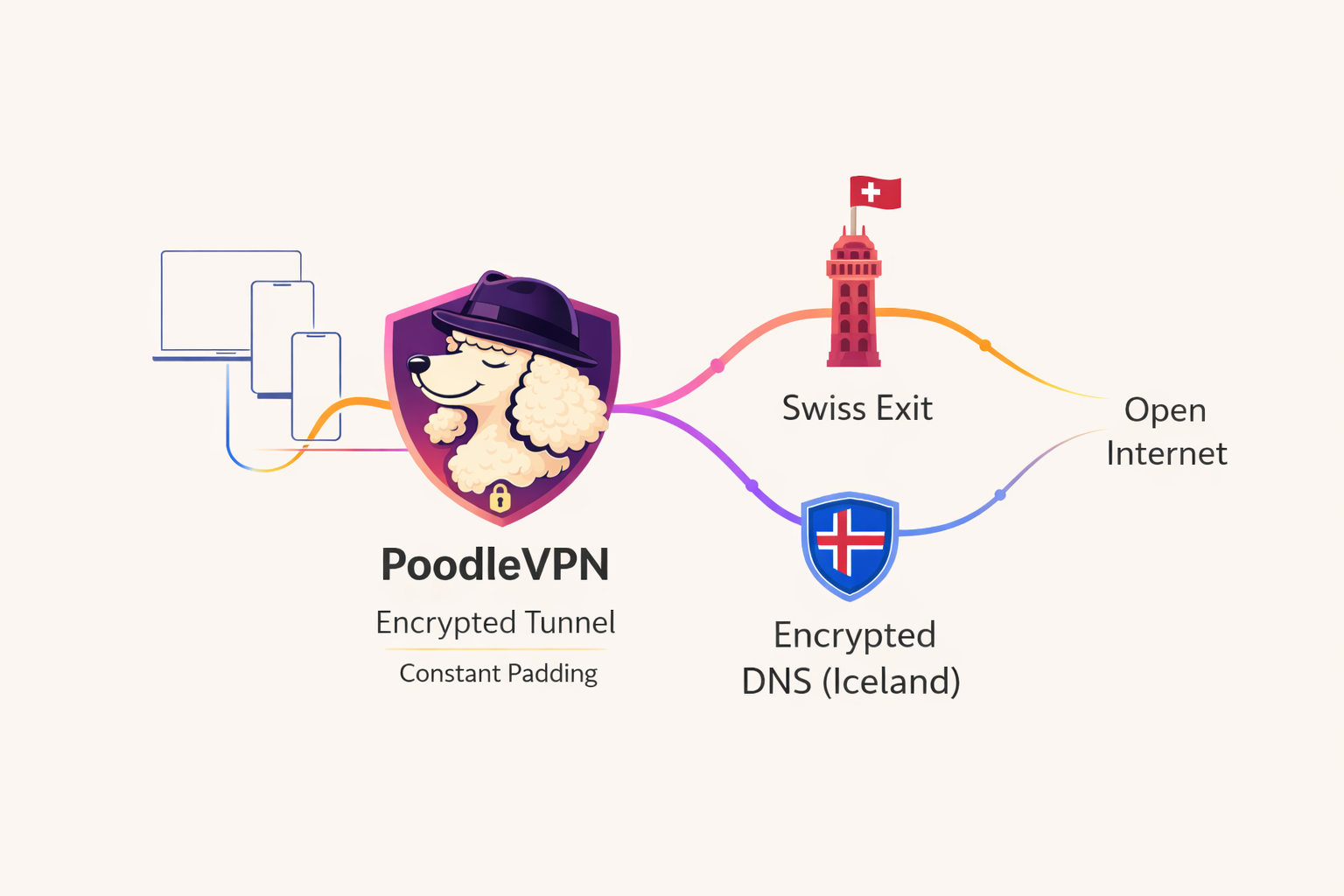
PoodleVPN is a deliberately minimal VPN architecture designed to eliminate identity surface area. No user accounts. No behavioral tracking. Just encrypted routing through jurisdiction-split infrastructure.
Understanding the fundamentals of virtual private network architecture
Every internet-connected device receives an IP address from its provider, creating a persistent network identifier that can be correlated across sessions.
Without encryption, internet service providers can monitor connection destinations, timing patterns, and protocol characteristics.
Encrypted tunnels route traffic through intermediary infrastructure, decoupling your identity from your network activity.
VPN exit nodes in different jurisdictions enable access to region-locked content and services.
Every architectural decision prioritizes reducing your digital footprint
Manual WireGuard key distribution eliminates user databases and authentication systems entirely.
No tracking pixels, no telemetry endpoints, no behavioral surveillance infrastructure.
Bare-metal server infrastructure in Switzerland provides strong legal privacy protections.
Domain resolution occurs over encrypted tunnel to servers in Iceland's privacy-friendly jurisdiction.
Critical infrastructure components span multiple countries, preventing single-point legal compromise.
Continuous dummy traffic reduces the effectiveness of timing correlation attacks.
Self-funded with no venture capital, advertisers, or external stakeholder pressures.
Compatible with proxy chains and Tor for users requiring enhanced anonymity.
Even when traffic is encrypted by a VPN, observable patterns such as bursts, pauses, and rate changes can still reveal information about activity and applications in use.
These patterns are increasingly relied upon for traffic analysis and correlation. Flatline is designed to reduce that surface.
Flatline is a traffic-shaping mode that enforces a constant outbound rate from the VPN tunnel. By flattening traffic spikes and idle gaps, it reduces observable variation and makes simple traffic analysis less reliable — without inspecting or reacting to user activity.
Flatline is intentionally deterministic. It does not adapt, classify, or analyze traffic. Instead, it minimizes metadata by ensuring that traffic exits the tunnel in a steady, uniform flow.
Learn More About Flatline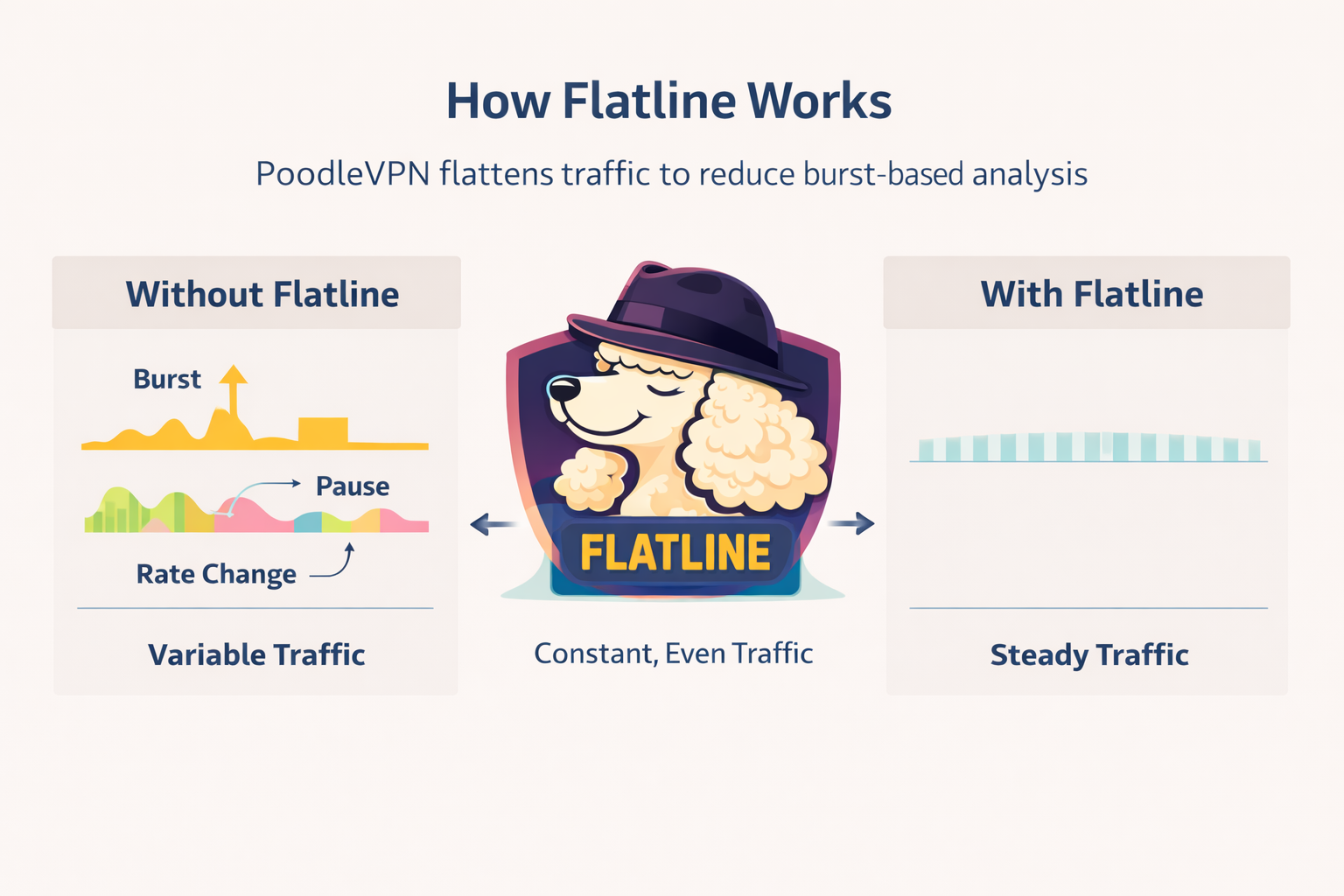
One simple plan. No upsells. No hidden fees. Cancel anytime.
All features included. No limits. No tiers.
Start Protecting Your PrivacyNo. PoodleVPN does not use accounts, usernames, or email addresses. Access is based on locally generated WireGuard keys only.
No traffic logs, no connection logs, no metadata retention. Our architecture makes logging technically unnecessary.
All traffic exits through physically controlled bare-metal servers in Switzerland, which provides strong legal privacy protections.
DNS resolution is performed through an encrypted tunnel to a private resolver located in Iceland, separate from the VPN exit node.
Optional constant-rate padding reduces burst patterns and makes simple traffic correlation less reliable by normalizing traffic flow.
Yes. PoodleVPN supports optional proxy layering and can be combined with Tor for higher-threat environments requiring enhanced anonymity.
Yes. There are no advertisers, analytics platforms, or external investors influencing infrastructure or policy decisions.
PoodleVPN uses WireGuard with manual key management for a minimal, auditable attack surface.